Real ways to hack VK to order, 100% guarantee
Proven ways to hack a VKontakte page
Today the market of spyware and software for hacking someone else's social network pages is represented by a huge number of solutions and offers, but not all of them are reliable and guarantee a successful hacking of an account. In this article, we will tell you what types of tools exist for hacking pages in the social network VKontakte and explain which of them are the most reliable.
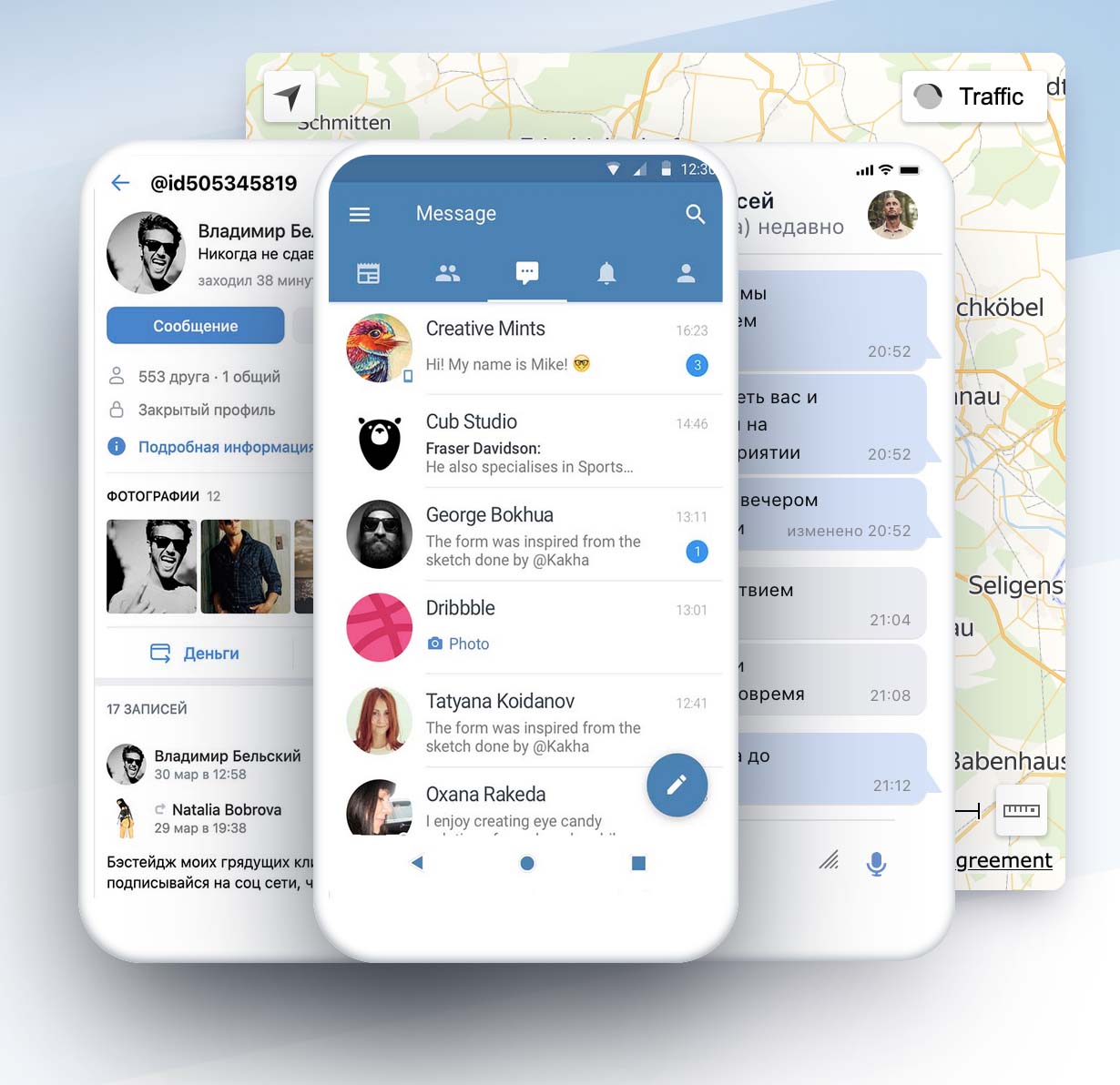
Optimal solution: VkTracker
Here we will not be original, almost all spyware reviews boil down to the fact that VzlomVK is the most reliable and functional solution. We explain why:
Reason #1. Reliability
n all tests, the application showed one hundred percent success in hacking real VK accounts. The software gave access to the account database, including messages, likes, page views, and other possible types of data the social network stores about its users. In addition, VzlomVK is quite reliable in terms of security, the Privacy Policy and Terms of Use clearly state that the data is stored on servers in encrypted form and is not used for advertising.
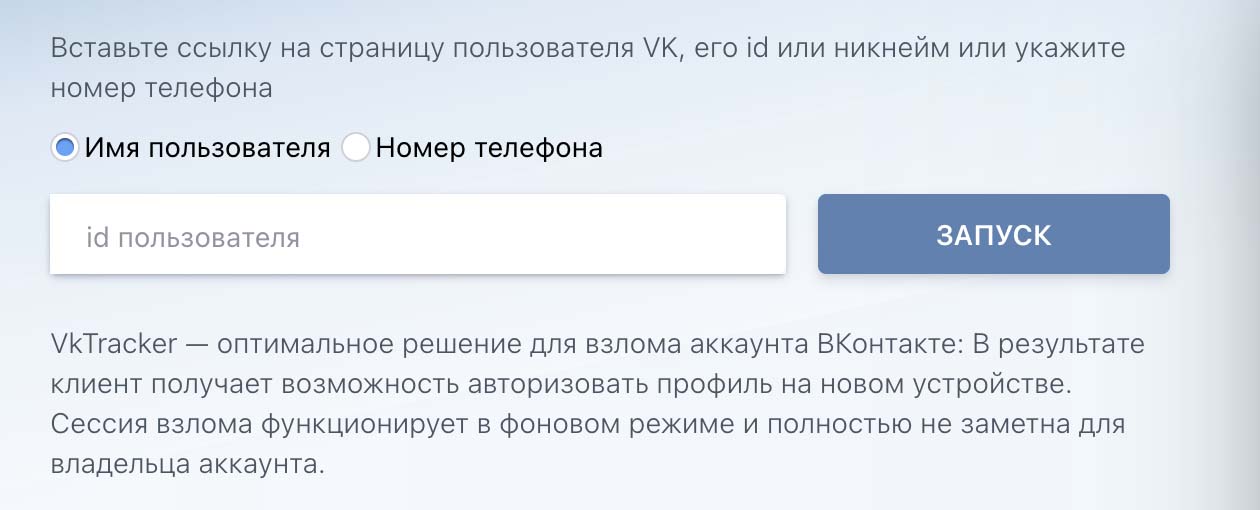
Reason #2. VkTracker - The easiest way to hack VK
The hack takes an average of 13 minutes. After that, in order to start working with the data, the user needs to log in to the Personal Cabinet of the user - a kind of Control Panel, which is very pleased with the optimized and extremely clear interface. VKTracker is a cross-platform web application, which means that in order to start tracking someone else's page VK you need to download and install anything, the solution works directly from the browser on any type of device.
Reason #3. Extensive functionality
Functionality is probably the main advantage of VzlomVK over its competitors. The application integrates all the functionality of the social network itself, and there are even some functions that are not available to VK users themselves - for example, the ability to download the account database to the device, how about it? Of all the solutions for online hacking VK, the only one gives the ability to search for messages or, for example, access to the data of the account advertising data (which can be super valuable information for businesses).
Reason #4. Regular updates
Recently a big update was released, significantly extending the functionality of the application. This is definitely a positive sign, confirming that the product is alive and growing. If you believe the information on the site, updates are released regularly, and the team is ready to listen to user suggestions.
Remote page hacking solutions
This category includes all solutions that exploit vulnerabilities in social networks' data transfer protocols, attacks on SS7 technology, social engineering, or password cracking technologies. For example, they can help users trying to figure out how to hack VK without access to iCloud and Jailbreak.
The bottleneck of this approach is the absence of any guarantees or any stable result-generating protocol. The main drawback is the rather low success rate of hacks: as a rule, such applications manage to hack only poorly protected accounts.
In general, remote hacking solutions can be divided into two categories:
Category #1. Applications whose success depends on account security
These solutions perform all of their claimed functionality, but the success of the hack depends on how well the account is protected. Typically, these applications have a good-faith refund policy for failed hacks.
Category #2. Applications that do not fully or partially perform their stated functions
For example, one of the tested solutions did hack the page database, but was not able to update it. To avoid such experiences, we recommend that you do some research on the reviews of the applications before you start using them.
Hacking apps pre-installed on your device
Here we will talk about full-fledged spyware that gives results, but requires access to the target user's smartphone. Such applications are a good choice for users who want to set parental control, or, for example, are looking for the easiest and fastest ways to hack VK on Android. We decided to describe separately the cases of hacking VK profiles from Android and iOS devices.
How to hack another person's VK to order if he uses an Android smartphone
With Android it is quite simple: you need to somehow transfer the APK file of the application to the target device and install it. The big disadvantage of such applications is that if the owner of the device is an advanced user, then, theoretically, he will be able to notice and track surveillance.
How to hack another person's VK to order if he uses an iOS smartphone
iOS devices for installing spyware require mandatory access to iCloud or Jailbreak, which, to be frank, requires a lot more dancing around than hacking a VK page. Moreover, this approach is not safe at all.
